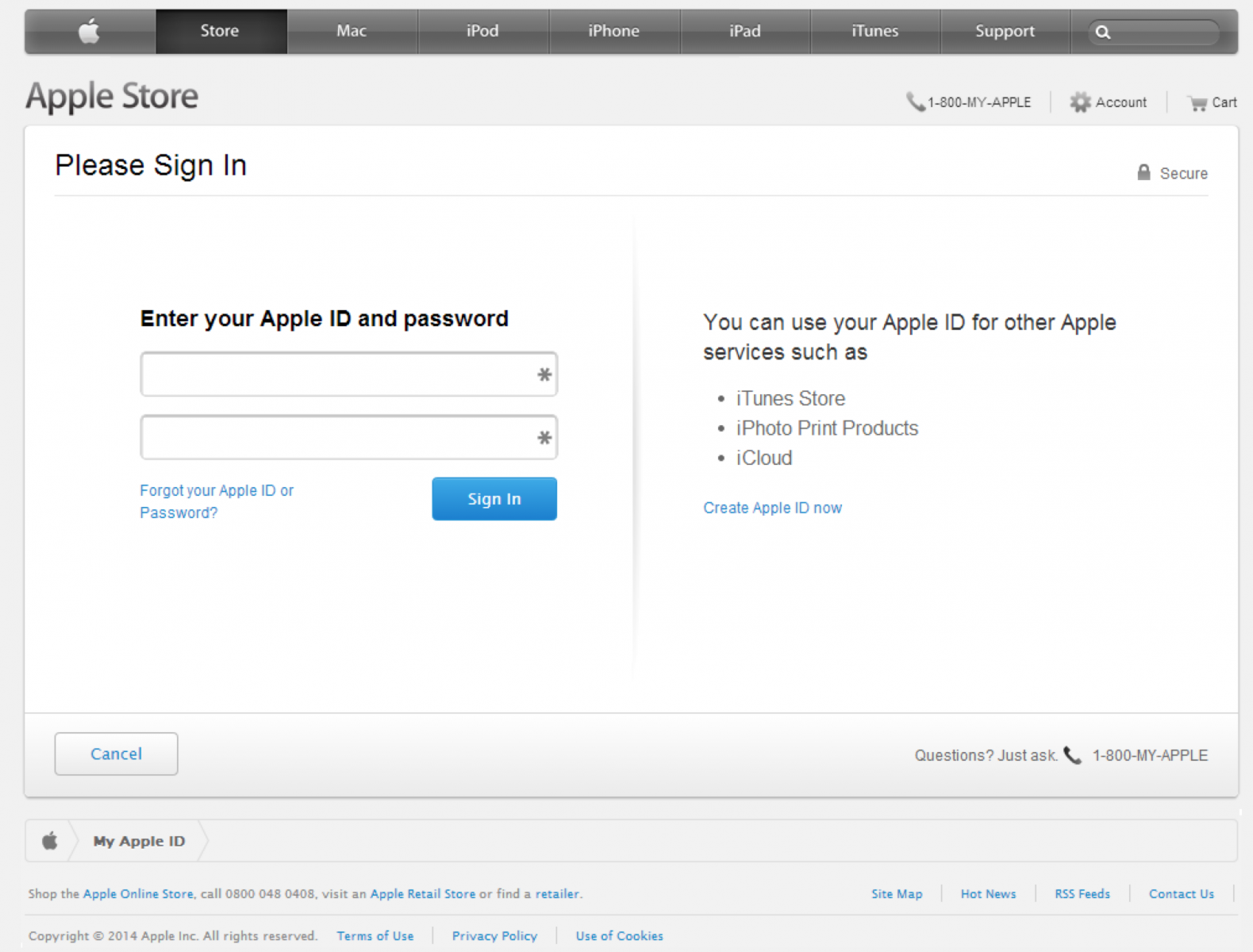
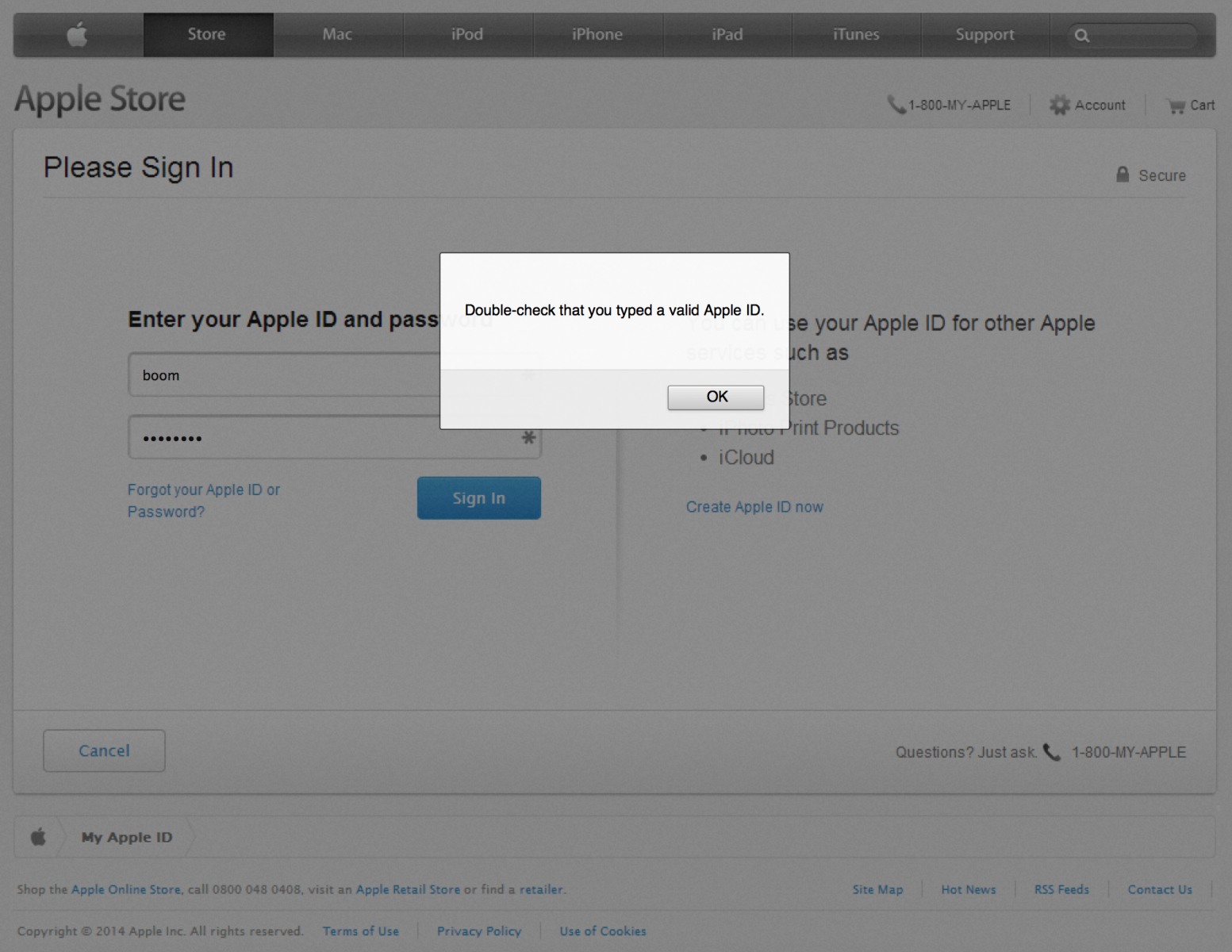
ISC user Craig Cox wrote in alerting us of a fairly sophisticated phishing campaign that is currently in progress. The website appleidconfirm.net has a seeminglyrealistic Apple login page that is being sent out by email.
The site even includes JavaScript code which validates your Apple ID as an email in an attempt to obtain only valid credentials.
Upon submitting what it considers valid credentials, you're redirected to the /?2 page of the site which contains another form which appears to be Apple's site:
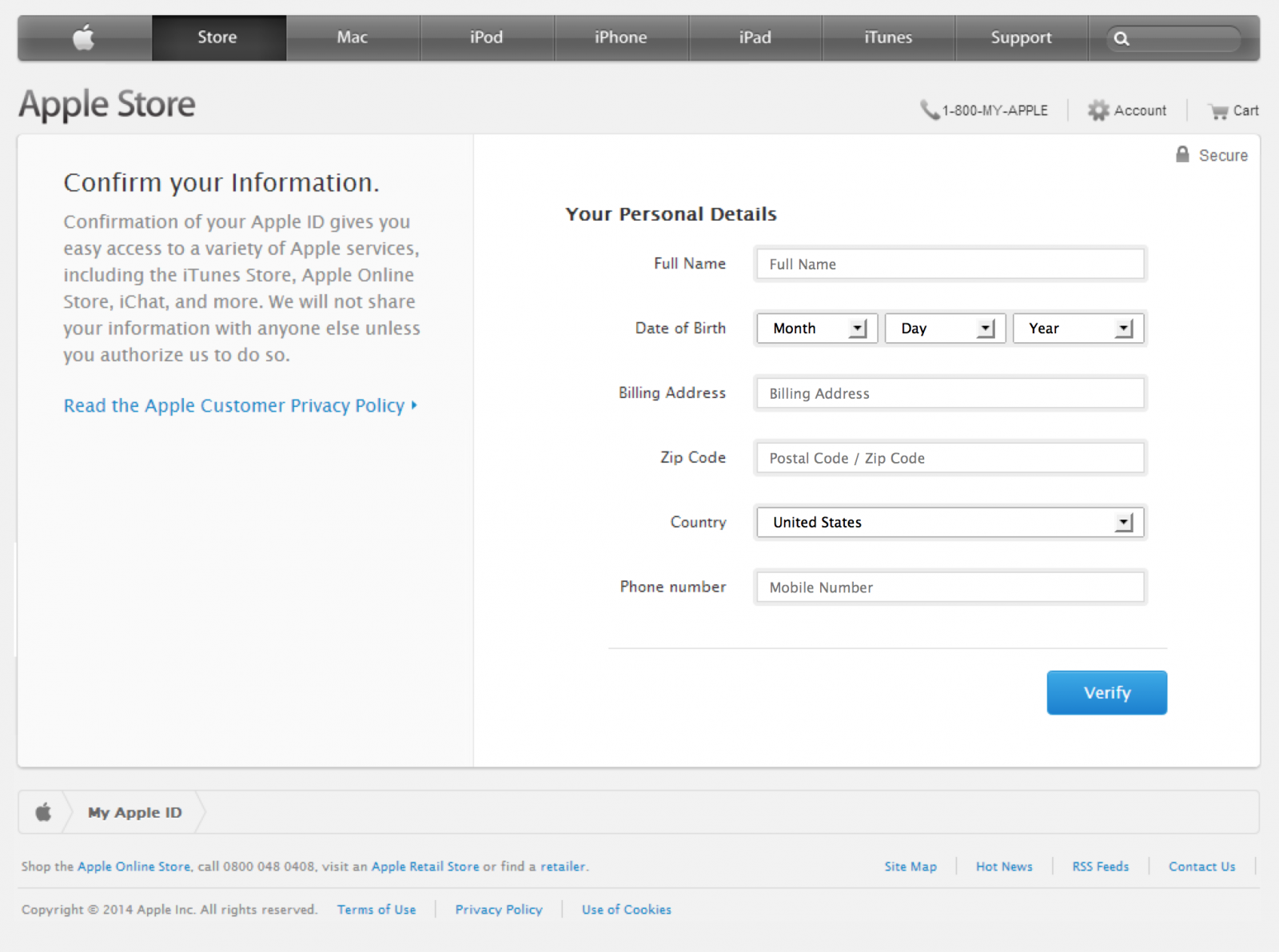
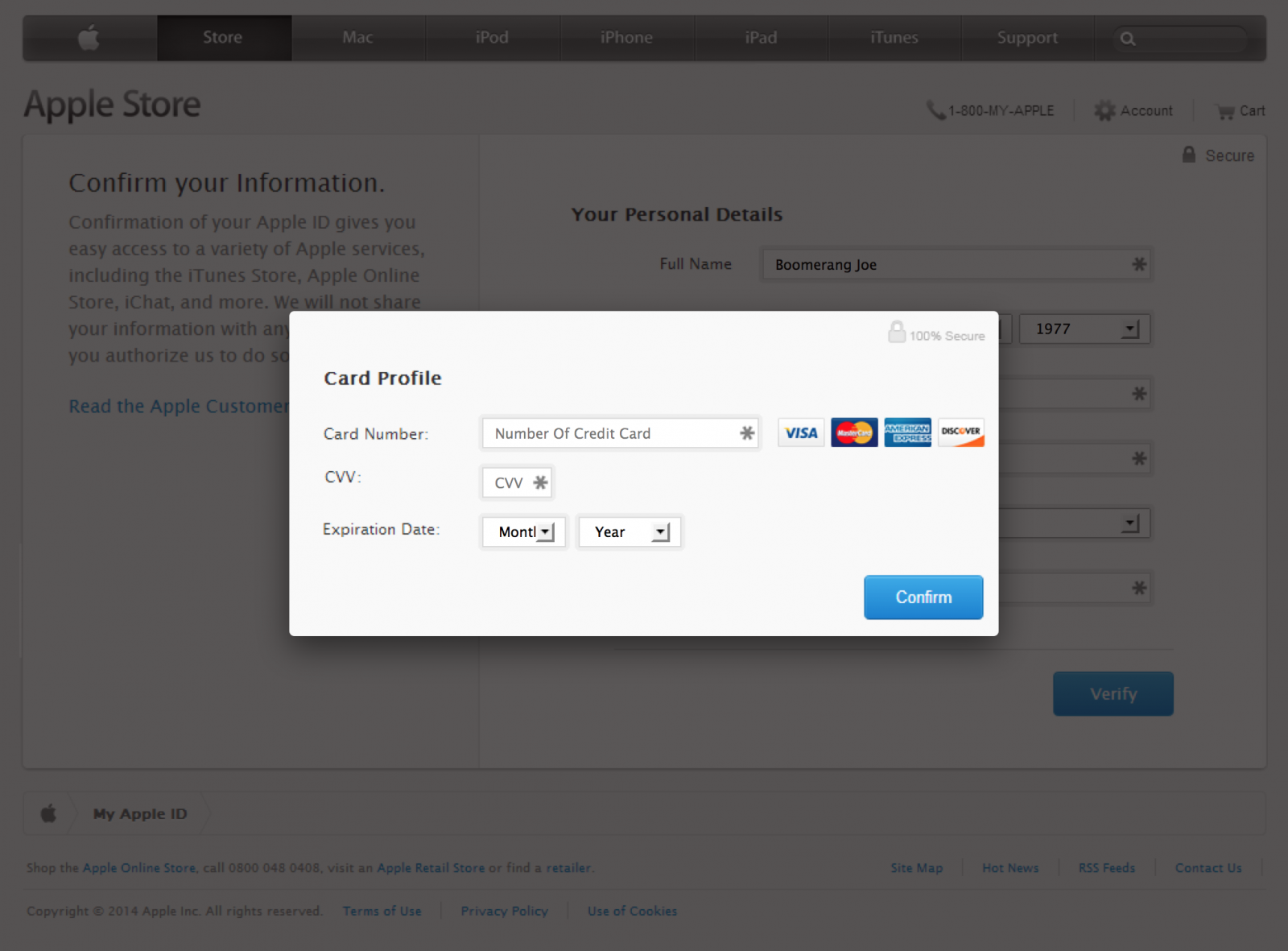
At this stage the site is collecting personal details about the account holder which may aid them in making changes to the account or stealing the victim's identity. After submitting precious personal information, it's now time to give them your credit card information:
Only after supplying a valid Visa, Mastercard, American Express or Discover card number are you forwarded to the /?3 "Success" page.
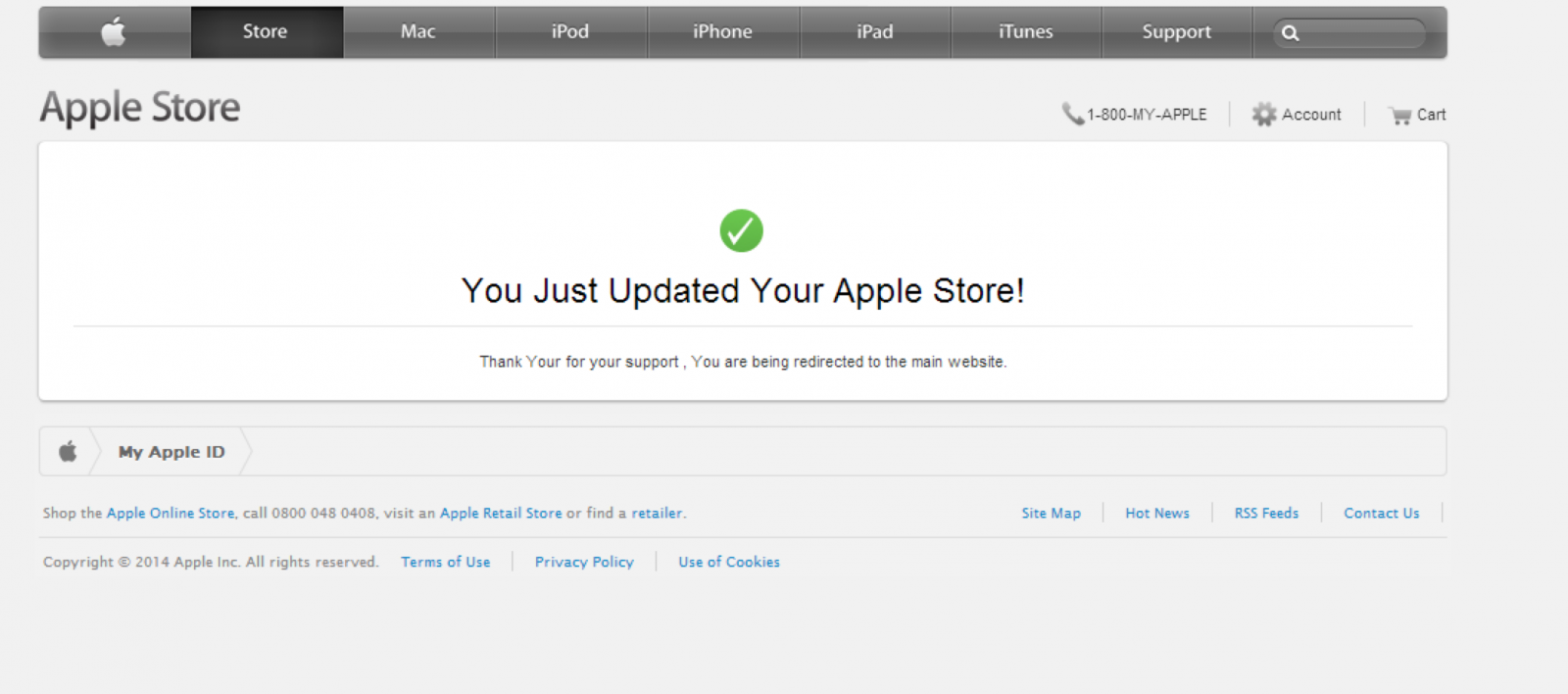
Finally, after a just a couple of seconds on this page (before you have a chance to click one of the links which are actually a screenshot image of the real Apple site without any functional links) you are redirected to the real apple.com. At this point the attacker would have obtained all the necessary information to exploit the victim, and the victim would have absolutely no idea how this happened. Clever!
Technical Analysis
We're able to observe or infer several things through a quick analysis.
First of all, we can observe that the site is running on PHP:
Set-Cookie: PHPSESSID=4b2be321acb0eac806780b7cd3ae1ba8;In the phishing emails, they have /e=6256734589233312746396443f323368 appended to the URL. It's not clear what this parameter does, and may just be some form of tracking identifier. (If you have better ideas as to what this might be, please share in the comments.)
We can also see that the site is hosted by Lycos with a domain registered just a day ago via Tucows.
Looking at the front-end of the site, we can see that the phishers didn't actually replicate the full HTML/CSS page but rather overlayed screenshots of the real apple.com with forms. This is how they manage to so accurately mimic the appearence of the target site without affording much effort into the front-end development. The background screenshot of apple.com used on their main page can be seen at http://www.appleidconfirm.net/img/main.png
Lastly, we can see that the site is not using HTTPS. This is a key differentiator from the true apple.com login page which does utilize HTTPS. Yet another reason to pay close attention to the URL bar in your browser.
Mitigation
Obviously it's not very difficult to craft a successful phishing campaign, but from a technological standpoint it's difficult to thwart them. So, what can we do? We should invest in awareness through education. That means reconsidering the amount of time and budgeting you set aside to train the less less-technical staff about phishing and social engineering. Informally, it may be time to sit down with that friend or family member who keeps sending you ads for weight loss because they have fallen victim to the latest phish. Knowledge is power.
Finally, when you see a phish in progress take the time to write a few abuse emails to the relevant providers. (and forward the phish to us!)
'Security_News > 해외보안소식' 카테고리의 다른 글
| Data-stealing Snoopy drone unveiled at Black Hat (0) | 2014.03.28 |
|---|---|
| The Russia-Ukraine Cyber Front Takes Shape (0) | 2014.03.28 |
| malware hijacks android mobile devices to mine (0) | 2014.03.28 |
| new platform protects data from arbitrary sever compromises (0) | 2014.03.28 |
| 이전 버전의mac 사용자에 대한 5가지 보안 tip (0) | 2014.03.27 |