728x90
Reader Ronnie provided us today a packet capture with a very interesting situation:
- Several packets are arriving, all ICMP echo request from unrelated address:
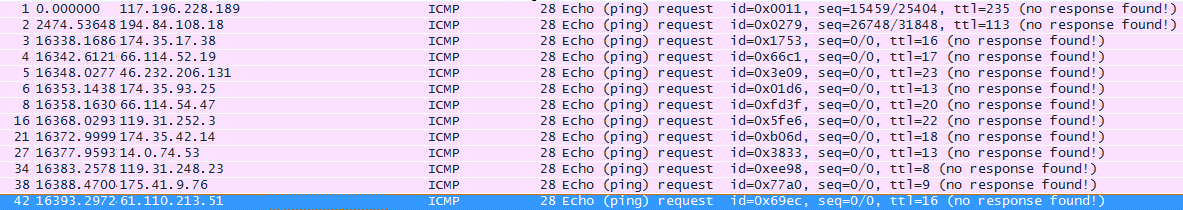
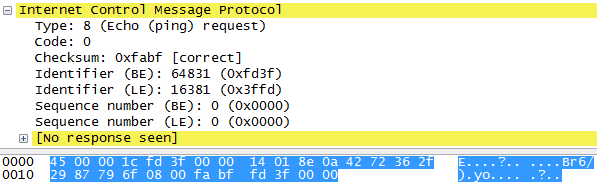
- All ICMP packets being sent to the destination address does not have data, leaving the packet with the 20 bytes for the IP header and 8 bytes for the ICMP echo request without data
- All the unrelated address sent 6 packets: One with normal TTL and 5 with incremental TTL:
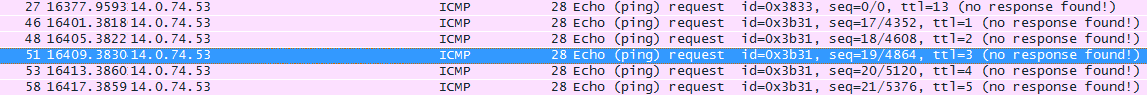
Seems to be those packets are trying to map a route, but in a very particular way. Since there are many unrelated IP addresses trying to do the same, maybe something is trying to map routes to specific address to do something not good. The destination IP address is an ADSL client.
Is anyone else seeing these kind of packets? If you do, we definitely want to hear from you. Let us know!
728x90
'malware ' 카테고리의 다른 글
| 진화하는 'Nuclear Exploit Kit "Silverlight에 존재하는 취약점도 이용 (0) | 2014.09.27 |
|---|---|
| FinFisher Malware Dropper Analysis (0) | 2014.09.21 |
| 신종 악성 코드를 발견. 이름하여 "Linux / GoARM.Bot"했습니다 (0) | 2014.09.20 |
| sraeli Security Think Tank Website Compromised And Serving Sweet-Orange Exploit Kit (0) | 2014.09.19 |
| Exploiting Ammyy Admin – developing an 0day (0) | 2014.09.19 |